Quantum computing, AI-powered attacks, and post-quantum standardization have fundamentally shifted the encryption landscape. This guide covers every major algorithm class and what the 2024 NIST post-quantum standards mean for the future of data security.
An encryption algorithm is a mathematical procedure that transforms readable plaintext into unreadable ciphertext using a secret key. Only those who possess the correct key can reverse the process and recover the original data. Encryption algorithms are the foundation of digital security: they protect cryptocurrency wallets, banking transactions, private communications, government records, and every HTTPS connection made across the internet. Modern algorithms are classified as symmetric (one shared key), asymmetric (public/private key pair), or hybrid systems that combine both approaches.
Key Takeaways (2025/2026)
- AES-256 remains the global standard for symmetric encryption with no known practical attacks, including against quantum computers at that key length.
- NIST finalized its first post-quantum cryptography (PQC) standards in August 2024: ML-KEM, ML-DSA, and SLH-DSA are now official federal standards.
- Triple DES (3DES) was formally deprecated by NIST in 2023 and is being retired across all legacy systems.
- RSA-2048 and ECC remain secure today but are considered quantum-vulnerable; organizations are advised to begin migration planning toward PQC algorithms.
- Fully homomorphic encryption (FHE) has seen major commercial deployments since 2023, enabling secure cloud computation on encrypted data.
- Quantum Key Distribution (QKD) networks are now operational in China, Europe, and Japan, providing information-theoretically secure key exchange.
- Bitcoin uses secp256k1 ECC and SHA-256; both face long-term quantum risk, prompting active blockchain-level PQC migration research.
As our world becomes increasingly digital, protecting sensitive information has never been more urgent. Encryption algorithms in cryptography have long been the backbone of data security, but the arrival of quantum computing, AI-driven cryptanalysis, and the NIST post-quantum standardization effort have fundamentally altered the landscape in 2024 and 2025.
This guide examines every major algorithm class, their current security status, real-world applications in cryptocurrency and finance, and what the shift toward post-quantum cryptography means for developers and traders alike.
What Are the Fundamental Concepts Behind Cryptography?
Cryptography is the science of securing information by transforming it into a format that is unreadable without the correct key or decoding method. It provides four core guarantees that underpin all digital security:
- Confidentiality: Only authorized parties can read the data.
- Integrity: Any tampering with data is detectable.
- Authentication: The identity of communicating parties can be verified.
- Non-repudiation: A sender cannot later deny having sent a message.
What is the core difference between symmetric and asymmetric cryptography?
In symmetric cryptography, both sender and recipient share a single secret key used for both encryption and decryption. This approach is fast and computationally efficient, making it ideal for encrypting large volumes of data. The primary challenge is securely distributing that shared key, especially over untrusted networks.
In asymmetric cryptography, two mathematically linked keys are used: a public key that anyone can access to encrypt data, and a private key that only the recipient holds to decrypt it. This elegantly solves the key distribution problem but requires significantly more computation. In practice, most secure systems use both: asymmetric encryption to exchange a session key, then symmetric encryption to protect the actual data.
Also Read: Quantitative Analysis of Crypto Markets
What Are the Major Symmetric Encryption Algorithms and Which Are Still Secure?
Symmetric encryption algorithms share a single key for both encryption and decryption. Their speed and efficiency make them the preferred choice for bulk data encryption, file storage, and real-time communications.

AES-256 and Quantum Computing: Grover’s quantum algorithm reduces AES-256 effective security to approximately 128 bits, which still represents an astronomically large search space. NIST has confirmed that AES-256 is considered sufficiently quantum-resistant for symmetric encryption, unlike RSA and ECC-based algorithms.
When should you use AES-128 versus AES-256?
AES-128 is faster and requires slightly less computational overhead, making it preferred for high-throughput applications like network encryption and disk I/O on constrained devices. AES-256 provides an extra security margin and is required for U.S. government top-secret classification and any application that needs to remain secure against long-term quantum threats. In cryptocurrency exchange platforms, AES-256 is the standard for encrypting user data, private key storage, and inter-service communications.
| Algorithm | Key Size | Block Size | Status (2026) | Primary Use |
|---|---|---|---|---|
| AES-128 | 128 bits | 128 bits | Secure | TLS, VPNs, device storage |
| AES-256 | 256 bits | 128 bits | Secure (quantum-resistant) | Government, finance, crypto |
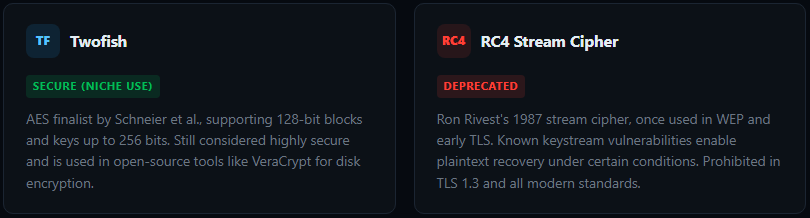
| Twofish | 128/192/256 bits | 128 bits | Secure | VeraCrypt, open-source tools |
| 3DES | 112/168 bits | 64 bits | Deprecated (2023) | Legacy financial systems only |
| DES | 56 bits | 64 bits | Broken | None (retired) |
| RC4 | 40–2048 bits | Stream | Broken | None (prohibited in TLS) |
Related reading: Smart Contracts: A Comprehensive Beginner’s Overview
What Are the Major Asymmetric Encryption Algorithms and How Do They Work?
Asymmetric encryption algorithms use a mathematically linked public/private key pair. The public key is freely distributed; the private key is kept secret. Data encrypted with the public key can only be decrypted with the corresponding private key, and vice versa for digital signatures.
How does RSA work and is it still secure in 2026?
RSA (Rivest-Shamir-Adleman), developed in 1977, bases its security on the computational difficulty of factoring the product of two large prime numbers. RSA-2048 and RSA-3072 remain secure against all known classical attacks in 2026. However, Shor’s quantum algorithm can factor these primes in polynomial time on a sufficiently powerful quantum computer. While such machines are not yet practically available, organizations handling data with a long secrecy horizon (government, healthcare, critical infrastructure) are already migrating to post-quantum alternatives.
Common applications include HTTPS/TLS for web security, PGP email encryption, digital certificate signing, and software distribution signing.
Also Read: Top 10 Largest Exchanges
What is Elliptic Curve Cryptography and why does crypto rely on it?
Elliptic Curve Cryptography (ECC) achieves the same security level as RSA with much smaller key sizes by exploiting the mathematical complexity of the Elliptic Curve Discrete Logarithm Problem (ECDLP). A 256-bit ECC key provides roughly equivalent security to a 3072-bit RSA key, meaning dramatically lower computational overhead.
Bitcoin uses the secp256k1 elliptic curve for private key generation and transaction signing. Ethereum uses the same curve. Every time you send a Bitcoin transaction, ECC proves ownership of funds without ever revealing the private key. ECDH (Elliptic Curve Diffie-Hellman) is used in TLS 1.3 for forward-secure session key exchange on every major crypto exchange platform.
Quantum Risk for Blockchain: Both RSA and ECC are considered quantum-vulnerable. A cryptographically relevant quantum computer running Shor’s algorithm could derive private keys from public keys on the Bitcoin and Ethereum networks. Active research into blockchain-level post-quantum migration is ongoing, though no timeline for a practical threat is currently established.
What is the Diffie-Hellman Key Exchange and when is it used?
Diffie-Hellman (DH), developed in 1976, allows two parties to establish a shared secret over a public channel without ever transmitting that secret. Each party selects a private key, computes a corresponding public value using an agreed prime and base, exchanges those public values, and each independently derives the same shared secret. This shared secret then seeds a symmetric encryption session.
Elliptic Curve Diffie-Hellman (ECDH) is the modern version, providing better security at smaller key sizes. ECDH is the basis for the perfect forward secrecy (PFS) key exchange in TLS 1.3, which means every browser session to a crypto exchange generates a unique key: compromising one session does not expose others.
| Algorithm | Key Size (Secure) | Quantum-Safe? | Status (2026) | Common Use |
|---|---|---|---|---|
| RSA-2048 | 2048+ bits | No | Transition to PQC | TLS certs, PGP, code signing |
| RSA-3072 | 3072 bits | No | Transition to PQC | High-assurance certificates |
| ECC secp256k1 | 256 bits | No | Secure (classical) | Bitcoin, Ethereum wallets |
| ECC P-256 | 256 bits | No | Secure (classical) | TLS 1.3, HTTPS |
| ECDH / ECDHE | 256–384 bits | No | Secure (classical) | TLS key exchange, PFS |
What Are NIST’s New Post-Quantum Cryptography Standards?
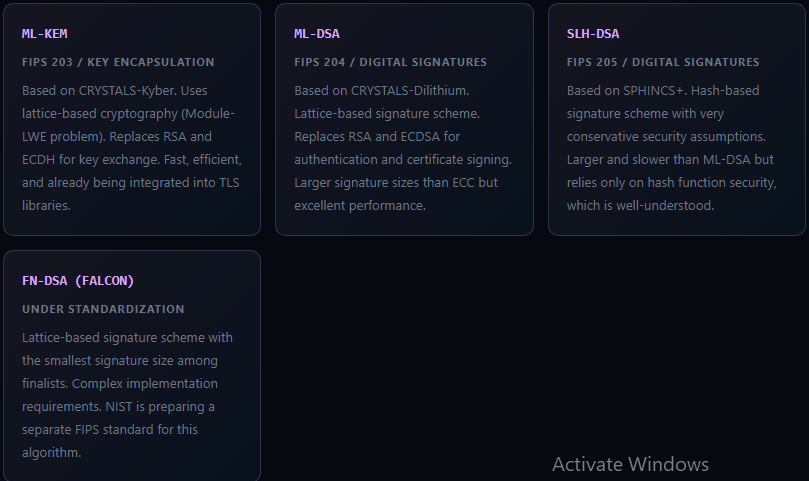
In August 2024, NIST finalized its first post-quantum cryptography (PQC) standards after an eight-year evaluation process. These algorithms are based on mathematical problems believed to be hard for both classical and quantum computers.
2024 NIST PQC Standards Finalized: NIST published FIPS 203 (ML-KEM), FIPS 204 (ML-DSA), and FIPS 205 (SLH-DSA) as official U.S. federal standards. Organizations handling sensitive data are now advised to begin migration planning. NIST also announced additional candidates under evaluation as backup options.
How Are Encryption Algorithms Used in Cryptocurrency Specifically?
What cryptographic primitives secure Bitcoin transactions?
Bitcoin relies on a layered combination of cryptographic tools. The secp256k1 elliptic curve generates public/private key pairs from which wallet addresses are derived. SHA-256 hashing secures the proof-of-work mining process and links blocks together in the blockchain. RIPEMD-160 combined with SHA-256 generates compressed public addresses. ECDSA (Elliptic Curve Digital Signature Algorithm) proves ownership when spending funds, allowing anyone to verify a signature using only the public key without exposing the private key.
How do crypto exchanges protect user data with encryption?
Reputable exchanges like UEEx, Binance, and Coinbase use AES-256 to encrypt stored user data including account information, KYC records, and private key material held in custody. All web and API connections use TLS 1.3 with ECDHE key exchange for perfect forward secrecy. Cold wallet private keys are typically stored in hardware security modules (HSMs) with additional encryption layers and multi-signature authorization requirements.
What is homomorphic encryption and how is it changing finance?
Homomorphic encryption (HE) allows arithmetic operations to be performed directly on encrypted data without decrypting it first. The output, when decrypted, matches the result you would get from operating on the original plaintext. This means a bank or exchange could run risk analysis or fraud detection on a user’s encrypted account data without ever seeing the raw figures.
Fully homomorphic encryption (FHE) has seen major commercial progress since 2022, with companies like Zama deploying FHE libraries for financial applications. Key performance bottlenecks remain for complex computations, but targeted FHE applications in KYC compliance and confidential AI-driven trading signals are now commercially viable as of 2025.
What is Quantum Key Distribution and where is it deployed?
Quantum Key Distribution (QKD) uses the principles of quantum mechanics to generate and distribute encryption keys with information-theoretic security: any interception of the key exchange physically alters the quantum states, making eavesdropping detectable. QKD networks are now operational in China (with thousands of kilometers of fiber), across several European cities via the EuroQCI initiative, and in commercial deployments in Japan and Singapore. While not yet practical for most organizations, QKD represents the long-term direction for ultra-high-security key exchange.
What Threats Are Pushing the Evolution of Encryption Algorithms?
How do side-channel attacks threaten encryption implementations?
Side-channel attacks exploit physical information leaked during the execution of an encryption algorithm, including timing variations, power consumption patterns, electromagnetic radiation, or even acoustic signals from hardware. A timing attack against an RSA implementation, for example, might infer the private key by measuring how long decryption takes for different inputs. These attacks target the implementation rather than the algorithm itself, making proper constant-time coding practices and hardware countermeasures essential regardless of which algorithm is chosen.
What role does AI play in modern cryptanalysis?
Machine learning is being applied to identify non-random patterns in ciphertext, improve differential and linear cryptanalysis, automate the discovery of implementation vulnerabilities, and generate realistic phishing attacks that bypass human review. So far, no AES or RSA-class algorithm has been broken by AI-assisted cryptanalysis, but the speed at which vulnerabilities in specific implementations are discovered has accelerated significantly since 2022.
Related reading: Mathematical and Cryptographic Principles in Blockchain
Frequently Asked Questions About Encryption Algorithms
What is the most widely used encryption algorithm today?
AES (Advanced Encryption Standard) is the most widely deployed symmetric encryption algorithm globally. AES-256 secures banking transactions, government communications, VPNs, smartphones, and cloud storage. It has no known practical attacks and is approved by NIST as the U.S. federal standard for top-secret data.
What is the difference between symmetric and asymmetric encryption?
Symmetric encryption uses a single shared key for both encrypting and decrypting data. It is fast and efficient, ideal for bulk data. Asymmetric encryption uses a public key to encrypt and a private key to decrypt. It solves the key distribution problem but is slower. Most real-world systems use both: asymmetric encryption to exchange a session key, then symmetric encryption to secure the actual data transfer.
Why is quantum computing a threat to current encryption?
Quantum computers running Shor’s algorithm can, in theory, factor the large prime numbers underlying RSA and break the discrete logarithm problems securing ECC and Diffie-Hellman. NIST finalized its first post-quantum cryptography standards in August 2024, including ML-KEM for key encapsulation and ML-DSA for digital signatures. Organizations are advised to begin migration planning now, especially for data with a long secrecy requirement.
What is post-quantum cryptography?
Post-quantum cryptography (PQC) refers to cryptographic algorithms designed to remain secure against attacks by quantum computers. NIST’s 2024 finalized PQC standards are based on lattice problems (ML-KEM, ML-DSA) and hash functions (SLH-DSA), believed hard for both classical and quantum computers. Migration to these standards is expected to accelerate through 2026 and beyond.
How is encryption used in cryptocurrency and blockchain?
Bitcoin uses secp256k1 ECC for wallet key generation and transaction signing, and SHA-256 for proof-of-work mining and block linkage. Ethereum uses the same elliptic curve. TLS encryption (AES + ECC/RSA) secures all communications between users and exchange platforms. Digital signatures prove asset ownership without revealing private keys.
Is AES-256 encryption unbreakable?
AES-256 has no known practical attack. A brute-force attempt would require more computational steps than there are atoms in the observable universe. It is considered quantum-resistant for symmetric operations at 256-bit key length because Grover’s quantum algorithm only halves effective security to 128 bits, which remains computationally infeasible to break.
What replaced DES as the encryption standard?
AES replaced DES as the U.S. federal encryption standard in 2001 after NIST selected the Rijndael algorithm in a public competition. DES was deprecated because its 56-bit key was cracked by brute force as early as 1999. Triple DES (3DES) served as a transitional standard but was formally deprecated by NIST in 2023 and is now being retired across all legacy systems.
What is homomorphic encryption and why does it matter?
Homomorphic encryption allows computations to be performed on encrypted data without first decrypting it. The decrypted result matches what you would get from operating on unencrypted data. This enables privacy-preserving cloud computing, confidential AI model training, and secure data analytics on sensitive financial datasets. Fully homomorphic encryption (FHE) has seen major commercial deployments since 2023.





