A 51% attack occurs when a single entity controls more than half of a blockchain’s mining power or staked tokens, enabling them to manipulate the transaction history, double-spend coins, and censor new transactions. As of 2025, a 24-hour attack on Bitcoin would cost nearly $53 million, making it practically impossible, but smaller proof-of-work chains remain highly vulnerable, as the Monero reorg of September 2025 demonstrated.
Key Takeaways
- A 51% attack occurs when a group or single entity controls more than 50% of a blockchain’s hash rate (computational power) or staked tokens.
- Attackers can double-spend transactions, censor new blocks, and reverse recent transaction history, but cannot steal funds from wallets they do not own or create coins out of thin air.
- Carrying out a 51% attack is challenging on large networks like Bitcoin (hashrate peaked at 1,160 EH/s in October 2025), but smaller blockchains with low hash rates remain primary targets.
- In September 2025, the Qubic mining pool executed Monero’s largest-ever blockchain reorganization, rolling back 18 blocks and invalidating approximately 118 transactions.
- Switching to Proof-of-Stake, implementing slashing penalties, and increasing confirmation requirements are the most effective defenses.
Related:What’s a Seed Phrase and Why Do You Need One?
What Is a 51% Attack?
A blockchain is an open-source, digital record book that securely and transparently records transactions and data across a distributed network of computers. Decentralization is its core feature. It means all participants can contribute to the network and earn rewards as it grows, while preventing any single person or authority from seizing control.
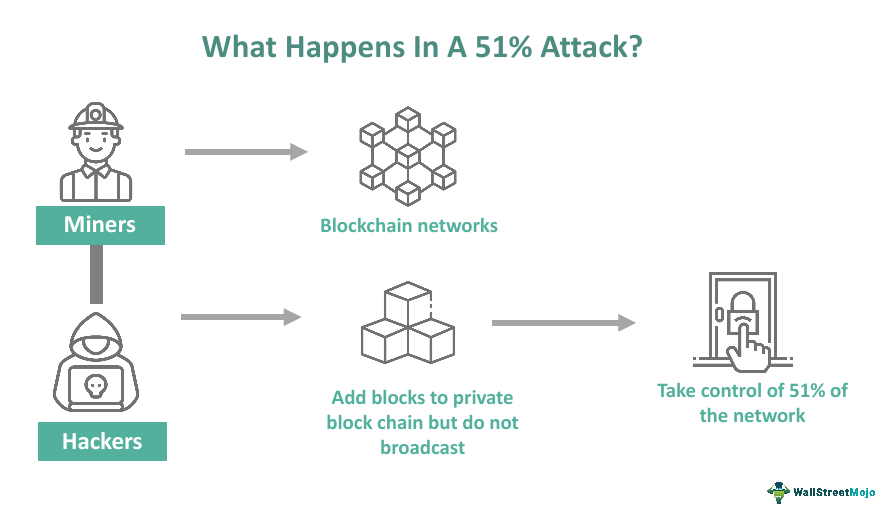
However, this decentralization only holds as long as no participant controls the majority of a network’s resources. A 51% attack occurs when a group of attackers or a single entity takes over more than half of a blockchain’s hash rate (computational power in Proof-of-Work systems) or staked tokens (in Proof-of-Stake systems).
In this attack, the controlling party can manipulate transactions on the affected blockchain, reverse recent history, and double-spend coins, but cannot steal funds from wallets they do not control or create new coins out of thin air.
Think of it like a company board vote. If one group owns more than 50% of the votes, they control every decision, regardless of what other shareholders want. In a blockchain, the group or entity that controls the majority of hashing power can execute transactions, exclude others, and rewrite recent history at will.
This attack is mainly performed on smaller networks with low hash rates, less usage, and minimal security measures. Larger blockchains like Bitcoin, Ethereum, and Solana have substantially more computational power and economic security, making attacks both technically difficult and financially irrational.
Related:Top Crypto Wallet Security Best Practices
How Did 51% Attacks Begin?
The first significant 51% attack incident can be traced to 2014, when the GHash.io pool (a popular Bitcoin mining pool that operated from 2013 to 2016) unintentionally controlled 55% of the Bitcoin network, triggering a 25% drop in Bitcoin’s value. Although the pool voluntarily reduced its power and pledged to stay below 40%, the incident exposed the risks of concentrated mining power for the first time.
In 2016, the cryptocurrencies Krypton and Shift, built on the Ethereum platform, were targeted by a group of hackers called “Team 51”. The attackers successfully double-spent and stole 22,000 coins through the Bittrex exchange.
The most notable early case occurred with Verge cryptocurrency (XVG) in 2018, compromised due to a code error. Verge’s multi-algorithm approach allowed attackers to exploit a bug sending false timestamped blocks to the network. Blocks were generated every second instead of every 30 seconds, allowing hackers to capture 99% of blocks during a three-hour attack. Officially, 250,000 tokens were stolen, though users reported the actual figure was closer to 4 million.
How Does a 51% Attack Work?
Carrying out a 51% attack is very expensive, energy-intensive, and technically demanding. This is why it is rarely attempted on large networks. On a Proof-of-Work blockchain, here is the sequence:
- Acquiring majority hash power: The attacker must control more than 50% of the blockchain’s total hash rate. This means investing in ASIC mining hardware, renting hash power from services like NiceHash, or persuading existing mining pools to collude.
- Mining a secret alternate chain: While the honest network continues building on the public chain, the attacker secretly mines their own version of the blockchain, not broadcasting it to other nodes.
- The double-spend setup: The attacker sends a transaction on the public chain (for example, depositing funds to an exchange), waits for it to be confirmed, then receives goods or withdraws funds.
- Broadcasting the longer chain: Because the attacker controls more than 50% of mining power, their private chain grows faster than the public one. When they broadcast it, the longest-chain rule means all honest nodes adopt it as the canonical record, erasing the original deposit transaction.
- The result: The attacker keeps both the goods or withdrawn funds and the original coins, which the private chain shows were never spent.
Energy context: According to the Columbia Climate School, mining Bitcoin requires up to 150 terawatts of energy per year, more than the annual consumption of countries like Finland and Argentina. This energy cost is itself one of Bitcoin’s primary defenses against 51% attacks.
For Proof-of-Stake blockchains like Ethereum, the equivalent attack requires controlling more than 51% of all staked tokens. This is dramatically more expensive because acquiring that volume of tokens drives up their price, and validators who act maliciously risk having their staked tokens slashed (destroyed) by the protocol.
What Are the Risks and Consequences of a 51% Attack?
1. Double-Spending
The primary and most financially damaging consequence. Attackers spend funds that have already been transacted, altering the blockchain to show the money was never sent so they can reuse it. An attacker spends 10 BTC on a purchase, uses their majority control to rewrite the chain so the transaction never occurred, and then spends the same 10 BTC again.
2. Denial-of-Service (DoS) Attack
The attacker takes control and blocks honest miners’ addresses, preventing them from regaining network control. This allows the attacker’s malicious transactions to become permanently embedded in the chain.
3. Transaction Reversal
The attacker blocks payments between users, disrupting the network’s regular operation, causing significant delays in transaction confirmations, and undermining confidence in the network’s reliability.
4. Reputational Damage
A 51% attack can severely damage a blockchain’s reputation, leading to a loss of trust among users and investors, a significant drop in the cryptocurrency’s value, and deterring new participants from joining the network.
What Are Real-World Examples of 51% Attacks?
May 2018
Bitcoin Gold (BTG)
Bitcoin Gold was victim to a 51% attack resulting in approximately $18 million in double-spends. This attack damaged the coin’s reputation significantly and highlighted its vulnerability due to its relatively small hash rate. Bitcoin Gold has since been a frequent target, with over 40 detected 51% attacks recorded by the MIT Digital Currency Initiative’s monitoring system.
August 2020
Ethereum Classic (ETC)
Ethereum Classic suffered one of its most significant attacks, with the attacker double-spending approximately $5.6 million worth of ETC. The network was hit twice within weeks. Following the attacks, Ethereum Classic raised its required confirmation count significantly to make future double-spends economically unviable for attackers.
December 2018
Vertcoin (VTC)
Vertcoin experienced a 51% attack resulting in a double-spend of approximately 603 VTC, equivalent to around $100,000 at the time. This attack demonstrated the vulnerability of smaller cryptocurrencies to rented hash power from services like NiceHash.
July 2019
Litecoin Cash (LCC)
Litecoin Cash’s Proof-of-Stake system was compromised in a 51% attack, resulting in a double-spend of less than $5,000. Though the financial impact was minimal, the attack demonstrated that even PoS systems require careful design to resist majority control.
Other notable examples include Feathercoin (FTC) and Verge (XVG).
Important: These attacks serve as a stark reminder that blockchain security is proportional to network size, hashrate diversity, and economic incentives. A network with low participation is not secure by virtue of being on the blockchain alone.
Related:Major Security Concerns in Crypto
What Happened with the Monero Attack in 2025?
The most significant 51% attack event of 2025 involved Monero (XMR) and the Qubic mining pool, led by former IOTA co-founder Sergey Ivancheglo. The incident unfolded in two phases during August and September 2025 and became one of the most-discussed blockchain security events in years.
How did Qubic accumulate majority hash power?
Qubic uses a “useful Proof-of-Work” model that repurposes Monero mining rewards. Miners contributing to Qubic’s pool earned Monero’s RandomX block rewards, which Qubic converted to USDT and used to buy and burn QUBIC tokens, creating financial incentives for miners to join. From mid-May to late July 2025, Qubic’s share of Monero’s global hashrate surged from under 2% to above 25%. By late August, it had accumulated over 51% of the network’s hash power.
What was the September 2025 reorg?
On September 14, 2025, Qubic executed Monero’s largest-ever blockchain reorganization. Starting at block 3,499,659 at 5:12 AM UTC and ending at block 3,499,676, the attack lasted approximately 36 to 43 minutes. Qubic privately mined a longer alternative chain using its majority hash power and then broadcast it to the network. Because Monero nodes follow the “longest chain wins” rule, all honest nodes adopted Qubic’s chain, orphaning 18 blocks and invalidating approximately 117 to 118 previously confirmed transactions.
Outcome: No confirmed double-spends or stolen funds were reported from the September 2025 Monero reorg. Most exchanges had raised their confirmation thresholds before the main attack. Monero’s price actually rose 5 to 7% on the day of the attack, though the event prompted Monero’s developers to begin researching solutions including rolling 10-block checkpoints and merge mining proposals.
The event demonstrated a core vulnerability of Proof-of-Work blockchains: any network where a single pool can accumulate sufficient economic incentives to attract majority hash power is at risk, regardless of its technical design. Monero’s CPU-friendly RandomX algorithm, designed to resist ASIC centralization, was not sufficient protection against a well-funded and economically motivated pool.
How Much Does a 51% Attack Cost in 2025?
The cost of a 51% attack scales directly with the size and hash rate of the target network. According to data from Crypto51 as of October 2025:
| Network | Consensus | Cost of 24-Hour Attack (Oct 2025) | Security Level |
|---|---|---|---|
| Bitcoin (BTC) | Proof-of-Work | ~$53 million | Extremely high |
| Ethereum (ETH) | Proof-of-Stake | Would require 51% of staked ETH (tens of billions) | Extremely high |
| Ethereum Classic (ETC) | Proof-of-Work | ~$144,000 | Moderate |
| Small altcoins | Proof-of-Work | As low as $1,000 to $5,000 | Low |
Bitcoin hash rate context: Bitcoin’s network hashrate peaked at approximately 1,160 exahashes per second (EH/s) in October 2025 and partially recovered to around 1,020 EH/s by early 2026. Controlling 51% of this would require billions of dollars in hardware and electricity costs that would likely exceed any possible profit from double-spending before the market reacted.
For smaller chains, attackers can rent hash power from services like NiceHash for the duration of an attack, avoiding the need to invest in permanent hardware. This makes short-term attacks against low-hashrate networks far more feasible. In 2025, a single cloud mining contract could give someone temporary majority control of a small chain’s network for under $5,000.
How Can Blockchains Be Protected Against 51% Attacks?

1. Switch to a Safer Consensus Algorithm
Some consensus algorithms, particularly Proof-of-Work, are more vulnerable to 51% attacks because they rely solely on mining power. Switching to Proof-of-Stake reduces this risk substantially. In PoS, attackers must own the majority of the network’s staked tokens rather than hash power. Acquiring this volume drives up token prices and, if the attack is detected, the protocol can slash the attacker’s stake, making the attack self-destructive.
Ethereum’s transition to PoS is the most prominent example. A theoretical 51% attack on Ethereum today would require owning more than half of all staked ETH, valued at tens of billions of dollars, with the risk of total loss through slashing.
2. Increase Confirmation Requirements
Exchanges and services should set confirmation requirements proportional to the blockchain’s security level. Bitcoin transactions are typically considered final after 6 confirmations. Following its attacks, Ethereum Classic raised its requirements to 40 or more. Highly vulnerable chains may require 100 or more. Dynamically adjusting thresholds based on real-time hash rate distribution also helps limit the damage of any single attack.
3. Implement Slashing and Penalty Systems
Implementing a penalty system, like slashing in Proof-of-Stake systems, significantly raises the stakes for attackers. Slashing confiscates tokens from malicious validators who attempt to manipulate the network, making attacks financially self-defeating. This deterrence is one of the strongest protections available.
4. Monitor for Chain Reorganizations
Active monitoring of the network for unusual chain reorganizations can detect an attack in progress. Systems that alert the community and exchanges when reorgs exceed a threshold (for example, more than 3 blocks) enable rapid response including temporary halting of deposits. The MIT Digital Currency Initiative’s reorg tracker detected over 40 deep reorganizations between 2019 and 2020 on multiple small chains.
5. Conduct Regular Security Audits
Regular audits and security checks help identify vulnerabilities in the blockchain protocol before attackers can exploit them. This includes checking for potential entry points for 51% attacks, reviewing mining pool concentration data, and addressing code vulnerabilities on an ongoing basis.
What Are Examples of Successful 51% Attack Prevention?
Claymore and Ethereum Classic (2019)
Claymore, a cryptocurrency mining pool, helped prevent a 51% attack on the Ethereum Classic blockchain by monitoring network activity for unusual patterns, alerting the community to take action, adjusting mining difficulty to make the attack more expensive, and collaborating with other mining pools to increase the overall hash rate.
Bitcoin Gold Network (2020)
The Bitcoin Gold network prevented several 51% attacks by implementing a real-time attack detection system, encouraging miners to increase the network’s aggregate hash rate, working with exchanges to implement higher confirmation requirements and additional security measures, and deploying regular software updates to patch vulnerabilities.
Monero Community Response (2025)
Following the September 2025 Qubic reorg, Monero’s developer team held a dedicated meeting on September 17 to address mining pool centralization. The Monero Research Lab began preparing a full postmortem and discussed proposals including rolling 10-block checkpoints, merge mining with larger networks, and economic incentives to punish selfish mining. Most exchanges had proactively raised their confirmation thresholds before the main attack, limiting the practical damage.
Related:How Blockchain Sharding Boosts Scalability and Efficiency
What Does the Future of 51% Attack Defense Look Like?
Blockchain technology promises security and immutability, but it is not perfect. 51% attacks expose the delicate balance between decentralization and security, highlighting the need for constant vigilance in any blockchain network.
The Monero incident of 2025 proved that even well-established, privacy-focused PoW chains with ASIC-resistant algorithms are not immune if economic incentives allow a single pool to accumulate majority hash power. The most robust long-term defenses remain increasing network participation, migrating to consensus mechanisms with built-in finality, implementing aggressive slashing penalties, and maintaining active monitoring infrastructure.
By acknowledging these vulnerabilities and addressing them proactively, blockchain networks can be hardened, ensuring the integrity and trustworthiness of the ecosystem for all participants.
Frequently Asked Questions
What is a 51% attack?
A 51% attack occurs when a single entity or coordinated group gains control of more than 50% of a blockchain’s mining hash rate (in Proof-of-Work networks) or staked tokens (in Proof-of-Stake networks). With majority control, the attacker can manipulate transaction history, double-spend coins, and censor new transactions, but cannot steal coins from wallets they do not own.
How much does a 51% attack on Bitcoin cost in 2025?
According to Crypto51 data from October 2025, a 24-hour 51% attack on Bitcoin would cost nearly $53 million. Bitcoin’s hashrate peaked at approximately 1,160 exahashes per second in October 2025, making it practically impossible for any single actor to execute such an attack profitably before the market reacted by crashing the coin’s value.
Has Bitcoin ever been successfully 51% attacked?
No. Bitcoin has never suffered a successful 51% attack. Its enormous hash rate and the prohibitive cost of acquiring majority mining power make such an attack economically irrational. Smaller proof-of-work coins such as Ethereum Classic, Bitcoin Gold, Vertcoin, and Monero have been the targets of real-world 51% attacks.
What happened with the Monero reorg attack in 2025?
In August and September 2025, the Qubic mining pool accumulated over 51% of Monero’s hashrate. On September 14, 2025, Qubic executed Monero’s largest-ever blockchain reorganization, rolling back 18 blocks and invalidating approximately 118 previously confirmed transactions. The attack lasted around 43 minutes. No confirmed double-spends or stolen funds were reported, but the event exposed the vulnerability of Monero’s proof-of-work consensus to mining centralization driven by economic incentives.
What is double-spending in a 51% attack?
Double-spending is the core exploit of a 51% attack. The attacker sends cryptocurrency to a target such as an exchange, waits for confirmations, receives goods or withdraws funds, then uses majority hash power to mine an alternate chain that does not include the original transaction. When this longer private chain is broadcast, it becomes the canonical record and the original payment is reversed, allowing the attacker to spend the same coins again.
How can blockchains protect against 51% attacks?
Key defenses include switching from Proof-of-Work to Proof-of-Stake consensus, which replaces hash power with economic stake; implementing slashing penalties that destroy attacker funds; increasing confirmation requirements for large deposits; monitoring for chain reorganizations; encouraging mining decentralization; and conducting regular security audits. Proof-of-Stake systems make attacks much more expensive because an attacker needs majority staked tokens and risks losing them entirely through slashing.
Can a 51% attack happen on proof-of-stake blockchains?
Yes, but it is far harder and more expensive. A 51% attack on a PoS blockchain requires controlling more than half of all staked tokens, which drives up the price of those tokens dramatically as the attacker buys them. If the attack is detected, the protocol can slash (destroy) the attacker’s entire stake, making the attack financially self-destructive.




